Understanding the Supply Chain and Risks of Large Language Model Applications Article Swipe
 YOU?
·
· 2025
· Open Access
·
· DOI: https://doi.org/10.48550/arxiv.2507.18105
YOU?
·
· 2025
· Open Access
·
· DOI: https://doi.org/10.48550/arxiv.2507.18105
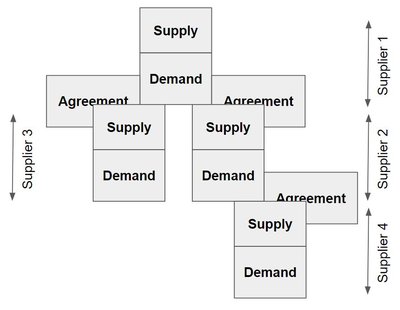
The rise of Large Language Models (LLMs) has led to the widespread deployment of LLM-based systems across diverse domains. As these systems proliferate, understanding the risks associated with their complex supply chains is increasingly important. LLM-based systems are not standalone as they rely on interconnected supply chains involving pretrained models, third-party libraries, datasets, and infrastructure. Yet, most risk assessments narrowly focus on model or data level, overlooking broader supply chain vulnerabilities. While recent studies have begun to address LLM supply chain risks, there remains a lack of benchmarks for systematic research. To address this gap, we introduce the first comprehensive dataset for analyzing and benchmarking LLM supply chain security. We collect 3,859 real-world LLM applications and perform interdependency analysis, identifying 109,211 models, 2,474 datasets, and 9,862 libraries. We extract model fine-tuning paths, dataset reuse, and library reliance, mapping the ecosystem's structure. To evaluate security, we gather 1,555 risk-related issues-50 for applications, 325 for models, 18 for datasets, and 1,229 for libraries from public vulnerability databases. Using this dataset, we empirically analyze component dependencies and risks. Our findings reveal deeply nested dependencies in LLM applications and significant vulnerabilities across the supply chain, underscoring the need for comprehensive security analysis. We conclude with practical recommendations to guide researchers and developers toward safer, more trustworthy LLM-enabled systems.
Related Topics
- Type
- preprint
- Language
- en
- Landing Page
- http://arxiv.org/abs/2507.18105
- https://arxiv.org/pdf/2507.18105
- OA Status
- green
- OpenAlex ID
- https://openalex.org/W4415233028
Raw OpenAlex JSON
- OpenAlex ID
-
https://openalex.org/W4415233028Canonical identifier for this work in OpenAlex
- DOI
-
https://doi.org/10.48550/arxiv.2507.18105Digital Object Identifier
- Title
-
Understanding the Supply Chain and Risks of Large Language Model ApplicationsWork title
- Type
-
preprintOpenAlex work type
- Language
-
enPrimary language
- Publication year
-
2025Year of publication
- Publication date
-
2025-07-24Full publication date if available
- Authors
-
Yujie Ma, Lili Quan, Xiaofei Xie, Qiang Hu, Jinming Yu, Yao Zhang, Sen ChenList of authors in order
- Landing page
-
https://arxiv.org/abs/2507.18105Publisher landing page
- PDF URL
-
https://arxiv.org/pdf/2507.18105Direct link to full text PDF
- Open access
-
YesWhether a free full text is available
- OA status
-
greenOpen access status per OpenAlex
- OA URL
-
https://arxiv.org/pdf/2507.18105Direct OA link when available
- Cited by
-
0Total citation count in OpenAlex
Full payload
| id | https://openalex.org/W4415233028 |
|---|---|
| doi | https://doi.org/10.48550/arxiv.2507.18105 |
| ids.doi | https://doi.org/10.48550/arxiv.2507.18105 |
| ids.openalex | https://openalex.org/W4415233028 |
| fwci | 0.0 |
| type | preprint |
| title | Understanding the Supply Chain and Risks of Large Language Model Applications |
| biblio.issue | |
| biblio.volume | |
| biblio.last_page | |
| biblio.first_page | |
| topics[0].id | https://openalex.org/T10028 |
| topics[0].field.id | https://openalex.org/fields/17 |
| topics[0].field.display_name | Computer Science |
| topics[0].score | 0.6614000201225281 |
| topics[0].domain.id | https://openalex.org/domains/3 |
| topics[0].domain.display_name | Physical Sciences |
| topics[0].subfield.id | https://openalex.org/subfields/1702 |
| topics[0].subfield.display_name | Artificial Intelligence |
| topics[0].display_name | Topic Modeling |
| topics[1].id | https://openalex.org/T10181 |
| topics[1].field.id | https://openalex.org/fields/17 |
| topics[1].field.display_name | Computer Science |
| topics[1].score | 0.6341000199317932 |
| topics[1].domain.id | https://openalex.org/domains/3 |
| topics[1].domain.display_name | Physical Sciences |
| topics[1].subfield.id | https://openalex.org/subfields/1702 |
| topics[1].subfield.display_name | Artificial Intelligence |
| topics[1].display_name | Natural Language Processing Techniques |
| is_xpac | False |
| apc_list | |
| apc_paid | |
| language | en |
| locations[0].id | pmh:oai:arXiv.org:2507.18105 |
| locations[0].is_oa | True |
| locations[0].source.id | https://openalex.org/S4306400194 |
| locations[0].source.issn | |
| locations[0].source.type | repository |
| locations[0].source.is_oa | True |
| locations[0].source.issn_l | |
| locations[0].source.is_core | False |
| locations[0].source.is_in_doaj | False |
| locations[0].source.display_name | arXiv (Cornell University) |
| locations[0].source.host_organization | https://openalex.org/I205783295 |
| locations[0].source.host_organization_name | Cornell University |
| locations[0].source.host_organization_lineage | https://openalex.org/I205783295 |
| locations[0].license | |
| locations[0].pdf_url | https://arxiv.org/pdf/2507.18105 |
| locations[0].version | submittedVersion |
| locations[0].raw_type | text |
| locations[0].license_id | |
| locations[0].is_accepted | False |
| locations[0].is_published | False |
| locations[0].raw_source_name | |
| locations[0].landing_page_url | http://arxiv.org/abs/2507.18105 |
| locations[1].id | doi:10.48550/arxiv.2507.18105 |
| locations[1].is_oa | True |
| locations[1].source.id | https://openalex.org/S4306400194 |
| locations[1].source.issn | |
| locations[1].source.type | repository |
| locations[1].source.is_oa | True |
| locations[1].source.issn_l | |
| locations[1].source.is_core | False |
| locations[1].source.is_in_doaj | False |
| locations[1].source.display_name | arXiv (Cornell University) |
| locations[1].source.host_organization | https://openalex.org/I205783295 |
| locations[1].source.host_organization_name | Cornell University |
| locations[1].source.host_organization_lineage | https://openalex.org/I205783295 |
| locations[1].license | cc-by |
| locations[1].pdf_url | |
| locations[1].version | |
| locations[1].raw_type | article |
| locations[1].license_id | https://openalex.org/licenses/cc-by |
| locations[1].is_accepted | False |
| locations[1].is_published | |
| locations[1].raw_source_name | |
| locations[1].landing_page_url | https://doi.org/10.48550/arxiv.2507.18105 |
| indexed_in | arxiv, datacite |
| authorships[0].author.id | https://openalex.org/A5100585021 |
| authorships[0].author.orcid | https://orcid.org/0000-0002-2386-1482 |
| authorships[0].author.display_name | Yujie Ma |
| authorships[0].author_position | first |
| authorships[0].raw_author_name | Ma, Yujie |
| authorships[0].is_corresponding | False |
| authorships[1].author.id | https://openalex.org/A5113199390 |
| authorships[1].author.orcid | https://orcid.org/0000-0002-2757-5627 |
| authorships[1].author.display_name | Lili Quan |
| authorships[1].author_position | middle |
| authorships[1].raw_author_name | Quan, Lili |
| authorships[1].is_corresponding | False |
| authorships[2].author.id | https://openalex.org/A5084396416 |
| authorships[2].author.orcid | |
| authorships[2].author.display_name | Xiaofei Xie |
| authorships[2].author_position | middle |
| authorships[2].raw_author_name | Xie, Xiaofei |
| authorships[2].is_corresponding | False |
| authorships[3].author.id | https://openalex.org/A5070193548 |
| authorships[3].author.orcid | https://orcid.org/0000-0003-4758-8625 |
| authorships[3].author.display_name | Qiang Hu |
| authorships[3].author_position | middle |
| authorships[3].raw_author_name | Hu, Qiang |
| authorships[3].is_corresponding | False |
| authorships[4].author.id | https://openalex.org/A5100648209 |
| authorships[4].author.orcid | https://orcid.org/0000-0001-5933-9912 |
| authorships[4].author.display_name | Jinming Yu |
| authorships[4].author_position | middle |
| authorships[4].raw_author_name | Yu, Jiongchi |
| authorships[4].is_corresponding | False |
| authorships[5].author.id | https://openalex.org/A5100446992 |
| authorships[5].author.orcid | https://orcid.org/0000-0002-7672-0165 |
| authorships[5].author.display_name | Yao Zhang |
| authorships[5].author_position | middle |
| authorships[5].raw_author_name | Zhang, Yao |
| authorships[5].is_corresponding | False |
| authorships[6].author.id | https://openalex.org/A5040142424 |
| authorships[6].author.orcid | https://orcid.org/0000-0002-5592-7917 |
| authorships[6].author.display_name | Sen Chen |
| authorships[6].author_position | last |
| authorships[6].raw_author_name | Chen, Sen |
| authorships[6].is_corresponding | False |
| has_content.pdf | False |
| has_content.grobid_xml | False |
| is_paratext | False |
| open_access.is_oa | True |
| open_access.oa_url | https://arxiv.org/pdf/2507.18105 |
| open_access.oa_status | green |
| open_access.any_repository_has_fulltext | False |
| created_date | 2025-10-16T00:00:00 |
| display_name | Understanding the Supply Chain and Risks of Large Language Model Applications |
| has_fulltext | False |
| is_retracted | False |
| updated_date | 2025-11-06T06:51:31.235846 |
| primary_topic.id | https://openalex.org/T10028 |
| primary_topic.field.id | https://openalex.org/fields/17 |
| primary_topic.field.display_name | Computer Science |
| primary_topic.score | 0.6614000201225281 |
| primary_topic.domain.id | https://openalex.org/domains/3 |
| primary_topic.domain.display_name | Physical Sciences |
| primary_topic.subfield.id | https://openalex.org/subfields/1702 |
| primary_topic.subfield.display_name | Artificial Intelligence |
| primary_topic.display_name | Topic Modeling |
| cited_by_count | 0 |
| locations_count | 2 |
| best_oa_location.id | pmh:oai:arXiv.org:2507.18105 |
| best_oa_location.is_oa | True |
| best_oa_location.source.id | https://openalex.org/S4306400194 |
| best_oa_location.source.issn | |
| best_oa_location.source.type | repository |
| best_oa_location.source.is_oa | True |
| best_oa_location.source.issn_l | |
| best_oa_location.source.is_core | False |
| best_oa_location.source.is_in_doaj | False |
| best_oa_location.source.display_name | arXiv (Cornell University) |
| best_oa_location.source.host_organization | https://openalex.org/I205783295 |
| best_oa_location.source.host_organization_name | Cornell University |
| best_oa_location.source.host_organization_lineage | https://openalex.org/I205783295 |
| best_oa_location.license | |
| best_oa_location.pdf_url | https://arxiv.org/pdf/2507.18105 |
| best_oa_location.version | submittedVersion |
| best_oa_location.raw_type | text |
| best_oa_location.license_id | |
| best_oa_location.is_accepted | False |
| best_oa_location.is_published | False |
| best_oa_location.raw_source_name | |
| best_oa_location.landing_page_url | http://arxiv.org/abs/2507.18105 |
| primary_location.id | pmh:oai:arXiv.org:2507.18105 |
| primary_location.is_oa | True |
| primary_location.source.id | https://openalex.org/S4306400194 |
| primary_location.source.issn | |
| primary_location.source.type | repository |
| primary_location.source.is_oa | True |
| primary_location.source.issn_l | |
| primary_location.source.is_core | False |
| primary_location.source.is_in_doaj | False |
| primary_location.source.display_name | arXiv (Cornell University) |
| primary_location.source.host_organization | https://openalex.org/I205783295 |
| primary_location.source.host_organization_name | Cornell University |
| primary_location.source.host_organization_lineage | https://openalex.org/I205783295 |
| primary_location.license | |
| primary_location.pdf_url | https://arxiv.org/pdf/2507.18105 |
| primary_location.version | submittedVersion |
| primary_location.raw_type | text |
| primary_location.license_id | |
| primary_location.is_accepted | False |
| primary_location.is_published | False |
| primary_location.raw_source_name | |
| primary_location.landing_page_url | http://arxiv.org/abs/2507.18105 |
| publication_date | 2025-07-24 |
| publication_year | 2025 |
| referenced_works_count | 0 |
| abstract_inverted_index.a | 84 |
| abstract_inverted_index.18 | 154 |
| abstract_inverted_index.As | 19 |
| abstract_inverted_index.To | 91, 141 |
| abstract_inverted_index.We | 109, 127, 198 |
| abstract_inverted_index.as | 40 |
| abstract_inverted_index.in | 181 |
| abstract_inverted_index.is | 32 |
| abstract_inverted_index.of | 2, 13, 86 |
| abstract_inverted_index.on | 43, 61 |
| abstract_inverted_index.or | 63 |
| abstract_inverted_index.to | 9, 76, 203 |
| abstract_inverted_index.we | 95, 144, 168 |
| abstract_inverted_index.325 | 151 |
| abstract_inverted_index.LLM | 78, 105, 113, 182 |
| abstract_inverted_index.Our | 175 |
| abstract_inverted_index.The | 0 |
| abstract_inverted_index.and | 53, 103, 115, 124, 134, 157, 173, 184, 206 |
| abstract_inverted_index.are | 37 |
| abstract_inverted_index.for | 88, 101, 149, 152, 155, 159, 194 |
| abstract_inverted_index.has | 7 |
| abstract_inverted_index.led | 8 |
| abstract_inverted_index.not | 38 |
| abstract_inverted_index.the | 10, 24, 97, 138, 188, 192 |
| abstract_inverted_index.Yet, | 55 |
| abstract_inverted_index.data | 64 |
| abstract_inverted_index.from | 161 |
| abstract_inverted_index.gap, | 94 |
| abstract_inverted_index.have | 74 |
| abstract_inverted_index.lack | 85 |
| abstract_inverted_index.more | 210 |
| abstract_inverted_index.most | 56 |
| abstract_inverted_index.need | 193 |
| abstract_inverted_index.rely | 42 |
| abstract_inverted_index.rise | 1 |
| abstract_inverted_index.risk | 57 |
| abstract_inverted_index.they | 41 |
| abstract_inverted_index.this | 93, 166 |
| abstract_inverted_index.with | 27, 200 |
| abstract_inverted_index.1,229 | 158 |
| abstract_inverted_index.1,555 | 146 |
| abstract_inverted_index.2,474 | 122 |
| abstract_inverted_index.3,859 | 111 |
| abstract_inverted_index.9,862 | 125 |
| abstract_inverted_index.Large | 3 |
| abstract_inverted_index.Using | 165 |
| abstract_inverted_index.While | 71 |
| abstract_inverted_index.begun | 75 |
| abstract_inverted_index.chain | 69, 80, 107 |
| abstract_inverted_index.first | 98 |
| abstract_inverted_index.focus | 60 |
| abstract_inverted_index.guide | 204 |
| abstract_inverted_index.model | 62, 129 |
| abstract_inverted_index.risks | 25 |
| abstract_inverted_index.their | 28 |
| abstract_inverted_index.there | 82 |
| abstract_inverted_index.these | 20 |
| abstract_inverted_index.(LLMs) | 6 |
| abstract_inverted_index.Models | 5 |
| abstract_inverted_index.across | 16, 187 |
| abstract_inverted_index.chain, | 190 |
| abstract_inverted_index.chains | 31, 46 |
| abstract_inverted_index.deeply | 178 |
| abstract_inverted_index.gather | 145 |
| abstract_inverted_index.level, | 65 |
| abstract_inverted_index.nested | 179 |
| abstract_inverted_index.paths, | 131 |
| abstract_inverted_index.public | 162 |
| abstract_inverted_index.recent | 72 |
| abstract_inverted_index.reuse, | 133 |
| abstract_inverted_index.reveal | 177 |
| abstract_inverted_index.risks, | 81 |
| abstract_inverted_index.risks. | 174 |
| abstract_inverted_index.safer, | 209 |
| abstract_inverted_index.supply | 30, 45, 68, 79, 106, 189 |
| abstract_inverted_index.toward | 208 |
| abstract_inverted_index.109,211 | 120 |
| abstract_inverted_index.address | 77, 92 |
| abstract_inverted_index.analyze | 170 |
| abstract_inverted_index.broader | 67 |
| abstract_inverted_index.collect | 110 |
| abstract_inverted_index.complex | 29 |
| abstract_inverted_index.dataset | 100, 132 |
| abstract_inverted_index.diverse | 17 |
| abstract_inverted_index.extract | 128 |
| abstract_inverted_index.library | 135 |
| abstract_inverted_index.mapping | 137 |
| abstract_inverted_index.models, | 49, 121, 153 |
| abstract_inverted_index.perform | 116 |
| abstract_inverted_index.remains | 83 |
| abstract_inverted_index.studies | 73 |
| abstract_inverted_index.systems | 15, 21, 36 |
| abstract_inverted_index.Language | 4 |
| abstract_inverted_index.conclude | 199 |
| abstract_inverted_index.dataset, | 167 |
| abstract_inverted_index.domains. | 18 |
| abstract_inverted_index.evaluate | 142 |
| abstract_inverted_index.findings | 176 |
| abstract_inverted_index.narrowly | 59 |
| abstract_inverted_index.security | 196 |
| abstract_inverted_index.systems. | 213 |
| abstract_inverted_index.LLM-based | 14, 35 |
| abstract_inverted_index.analysis, | 118 |
| abstract_inverted_index.analysis. | 197 |
| abstract_inverted_index.analyzing | 102 |
| abstract_inverted_index.component | 171 |
| abstract_inverted_index.datasets, | 52, 123, 156 |
| abstract_inverted_index.introduce | 96 |
| abstract_inverted_index.involving | 47 |
| abstract_inverted_index.issues-50 | 148 |
| abstract_inverted_index.libraries | 160 |
| abstract_inverted_index.practical | 201 |
| abstract_inverted_index.reliance, | 136 |
| abstract_inverted_index.research. | 90 |
| abstract_inverted_index.security, | 143 |
| abstract_inverted_index.security. | 108 |
| abstract_inverted_index.associated | 26 |
| abstract_inverted_index.benchmarks | 87 |
| abstract_inverted_index.databases. | 164 |
| abstract_inverted_index.deployment | 12 |
| abstract_inverted_index.developers | 207 |
| abstract_inverted_index.important. | 34 |
| abstract_inverted_index.libraries, | 51 |
| abstract_inverted_index.libraries. | 126 |
| abstract_inverted_index.pretrained | 48 |
| abstract_inverted_index.real-world | 112 |
| abstract_inverted_index.standalone | 39 |
| abstract_inverted_index.structure. | 140 |
| abstract_inverted_index.systematic | 89 |
| abstract_inverted_index.widespread | 11 |
| abstract_inverted_index.LLM-enabled | 212 |
| abstract_inverted_index.assessments | 58 |
| abstract_inverted_index.ecosystem's | 139 |
| abstract_inverted_index.empirically | 169 |
| abstract_inverted_index.fine-tuning | 130 |
| abstract_inverted_index.identifying | 119 |
| abstract_inverted_index.overlooking | 66 |
| abstract_inverted_index.researchers | 205 |
| abstract_inverted_index.significant | 185 |
| abstract_inverted_index.third-party | 50 |
| abstract_inverted_index.trustworthy | 211 |
| abstract_inverted_index.applications | 114, 183 |
| abstract_inverted_index.benchmarking | 104 |
| abstract_inverted_index.dependencies | 172, 180 |
| abstract_inverted_index.increasingly | 33 |
| abstract_inverted_index.proliferate, | 22 |
| abstract_inverted_index.risk-related | 147 |
| abstract_inverted_index.underscoring | 191 |
| abstract_inverted_index.applications, | 150 |
| abstract_inverted_index.comprehensive | 99, 195 |
| abstract_inverted_index.understanding | 23 |
| abstract_inverted_index.vulnerability | 163 |
| abstract_inverted_index.interconnected | 44 |
| abstract_inverted_index.infrastructure. | 54 |
| abstract_inverted_index.interdependency | 117 |
| abstract_inverted_index.recommendations | 202 |
| abstract_inverted_index.vulnerabilities | 186 |
| abstract_inverted_index.vulnerabilities. | 70 |
| cited_by_percentile_year | |
| countries_distinct_count | 0 |
| institutions_distinct_count | 7 |
| citation_normalized_percentile |